

DevSecOps Recruitment Guide Europe (2026 Guide)
DevSecOps is no longer a “nice to have” capability in Europe. For cloud-native teams running Kubernetes, shipping daily via CI/CD pipelines, and operating under increasing regulatory scrutiny, security needs to be designed into delivery, not bolted on after incidents.
That shift is driving a sharp increase in devsecops recruitment europe projects, and it is also exposing a market reality: the best DevSecOps engineers are scarce, globally competed for, and often not actively job-seeking. If you are trying to hire DevSecOps engineers in Europe in 2026, you need a hiring plan that is technical, compliance-aware (NIS2, ISO 27001), and fast enough to close offers before counter-offers land.
If your search sits within a broader security org build-out, start with Optima’s pillar guide on Cybersecurity recruitment in Europe, then use the roadmap below to design, assess, and close DevSecOps hires with less risk.
What Is DevSecOps?
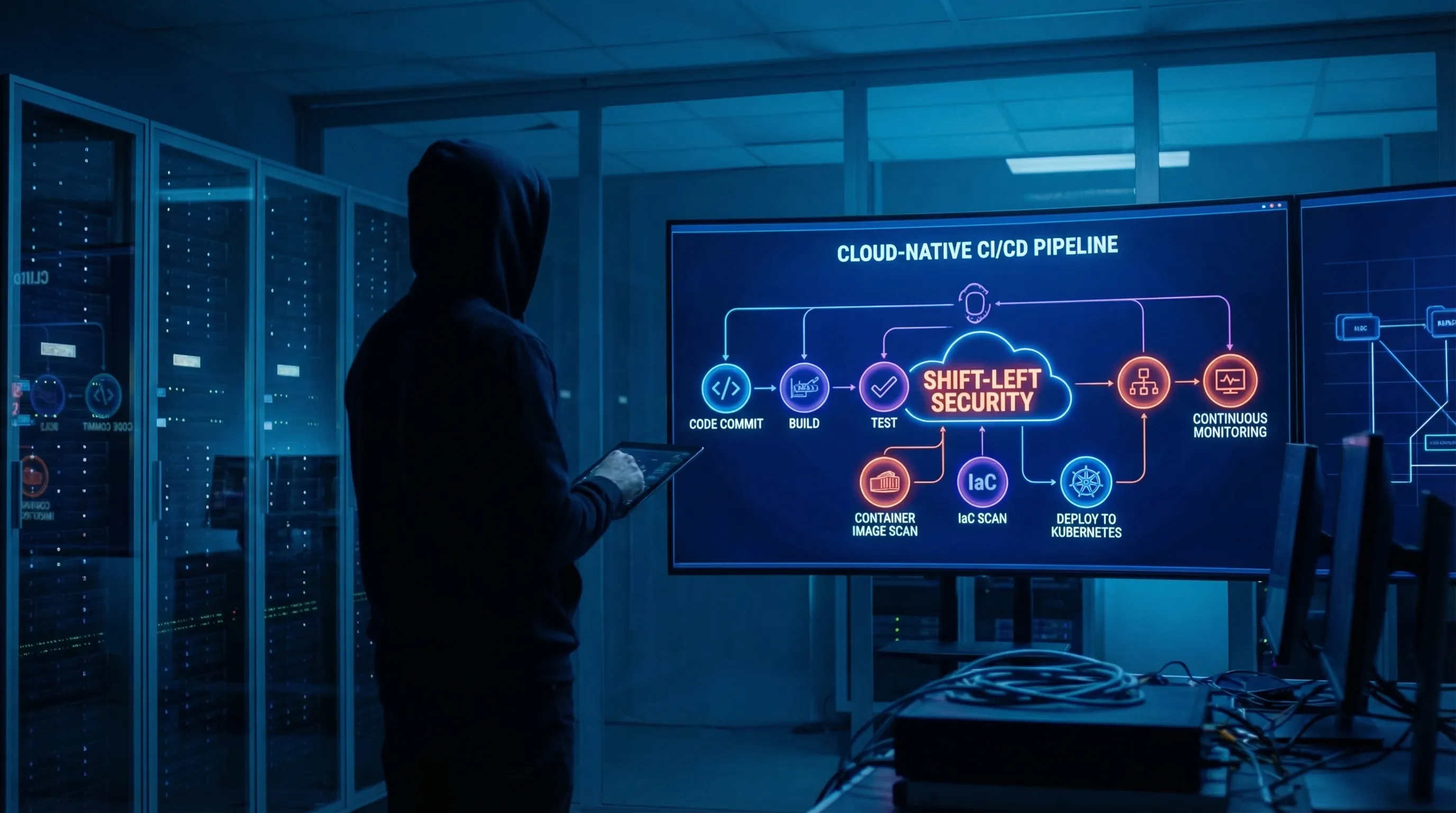
DevSecOps is an operating model that integrates security engineering, risk thinking, and security controls into the DevOps lifecycle, from design through build, deploy, and runtime. The goal is to make secure delivery repeatable and measurable, without slowing down release velocity.
DevOps vs DevSecOps
DevOps focuses on shortening delivery cycles and increasing reliability via automation, observability, and cross-functional collaboration. DevSecOps keeps those objectives, but adds a security dimension that is explicit and engineered:
- Threat modelling and secure design earlier in delivery
- Automated security testing embedded in CI/CD pipelines
- Secure configuration standards for cloud and containers
- Stronger identity and access patterns (often aligned to Zero Trust)
- Evidence for audit and compliance, not just “security intent”
Shift-left security in practice
“Shift-left security” means moving security controls and decision points closer to where code and infrastructure change happens, typically:
- Developers get fast feedback via SAST, dependency scanning, secrets detection, and policy checks.
- Platform teams make secure defaults easy (golden pipelines, approved base images, IaC modules).
- Security teams define guardrails and detection, and focus on exceptions and high-risk pathways.
Security integrated into CI/CD pipelines
In mature DevSecOps environments, CI/CD pipelines become a governance mechanism. Examples include:
- Enforcing signed artefacts and provenance (supply chain integrity)
- Scanning container images before release
- Scanning Infrastructure as Code (IaC) changes before apply
- Blocking deploys that fail policy-as-code checks
Structured summary: DevSecOps is the evolution of DevOps for cloud-native delivery under real threat pressure. It embeds “shift-left security” into CI/CD pipelines so security becomes continuous, automated, and auditable, rather than periodic and reactive.
Why DevSecOps Hiring Is Growing Rapidly in Europe
European demand is being driven by a mix of architecture change, threat economics, and compliance pressure.
First, cloud-native architectures have become the default for many scale-ups and modernised enterprises, and that usually means containers (Docker), orchestration (Kubernetes), IaC, and a reliance on managed services across AWS, Azure, and GCP. The attack surface is broader, and the misconfiguration risk is persistent.
Second, multi-cloud and hybrid-cloud operations are increasing. Even when a company claims “single cloud”, acquisitions, regional data requirements, and vendor constraints often create a multi-platform reality. That multiplies identity, policy, logging, and control plane complexity.
Third, regulatory expectations are rising. The NIS2 Directive has pushed cyber governance higher on executive agendas, and many organisations are translating that pressure into engineering hiring, not just GRC hiring. In parallel, ISO 27001 remains a common control framework for buyers and partners, especially in enterprise sales cycles.
Market observations we see repeatedly in 2026:
- Platform engineering teams are being asked to “own security outcomes” for shared infrastructure, not only uptime.
- Security leaders want controls that generate audit-ready evidence automatically (for example, pipeline logs, policy checks, change approvals).
- AI workloads and sensitive data in cloud environments are amplifying demand for cloud security and DevSecOps capability, especially around identity and segmentation.
Why DevSecOps Hiring Is More Complex Than Traditional DevOps
Hiring DevOps engineers is already hard in Europe, but security devops engineer hiring is harder for structural reasons.
1) Hybrid skill requirements (DevOps + Security + Cloud)
A credible DevSecOps engineer needs depth in at least two domains and fluency across three:
- DevOps delivery: CI/CD, release engineering, reliability, tooling automation
- Cloud security: IAM, network segmentation, logging, key management
- Modern infrastructure: Kubernetes, Docker, IaC, service-to-service identity
Candidates who can do this end-to-end are rare, and many are already in high-trust roles.
2) Security-first mindset is not just tooling
DevSecOps is not “run a scanner.” It requires threat thinking, secure-by-default design, and the ability to influence engineering behaviour. You are hiring judgement as much as you are hiring execution.
3) Limited senior talent pool
Europe’s DevSecOps talent shortage is most visible at senior level: people who have built secure delivery systems across multiple teams, handled real incidents, and can partner with CISOs, auditors, and platform leads.
4) Certification validation adds friction
Certifications can help signal baseline knowledge (for example, cloud security certs or Kubernetes security), but they are imperfect. Strong candidates often have uneven certification footprints, and weaker candidates can be “over-certified”. You still need technical evidence.
5) Salary inflation and global competition
DevSecOps talent is heavily competed for by US firms, security vendors, and European enterprises modernising under NIS2. As a result, salary expectations can rise faster than internal bands, and offers are frequently compared across borders.
Key Skills to Look for in DevSecOps Engineers
A useful way to run a DevSecOps hiring process is to assess skills by “control surface”, pipeline, containers, IaC, cloud platform, detection, and compliance. Below is a practical breakdown that aligns to real delivery work.
CI/CD pipeline security
Look for candidates who can secure pipelines, not just build them:
- Secure build patterns (ephemeral runners, least privilege, separation of duties)
- Artefact integrity (signing, verified provenance, controlled registries)
- Policy gates (what to block, what to warn on, how to manage exceptions)
- Secrets management in pipelines (rotation, scanning, prevention)
A strong candidate should be able to explain how they prevented “pipeline as the attacker’s path.”
Container security (Kubernetes, Docker)
DevSecOps engineers working in containerised environments should understand:
- Kubernetes RBAC, admission control, and workload identity
- Image hardening, minimal base images, vulnerability management
- Runtime controls (what to monitor, what to block, how to alert)
- Cluster and control plane risk (misconfigurations, exposed dashboards, etc.)
Expect them to talk in specifics: namespaces, network policies, pod security controls, and how they reduce blast radius.
Infrastructure as Code (Terraform, CloudFormation)
IaC is where misconfiguration risk becomes systemic. Assess whether the candidate can:
- Build reusable secure modules and guardrails
- Implement policy-as-code (for example, OPA-style checks)
- Integrate scanning into PR workflows
- Manage drift and change control without slowing delivery
They should be comfortable reviewing real Terraform diffs and explaining risk.
Cloud platform security (AWS, Azure, GCP)
Because most DevSecOps roles are effectively cloud security devsecops recruitment roles, confirm they can operate at the platform layer:
- IAM design patterns (role-based access, short-lived credentials, federation)
- Network controls (segmentation, private endpoints, egress control)
- Logging and monitoring baselines (control plane logs, audit trails)
- Key management and encryption patterns
Ask them how they would implement Zero Trust principles in cloud architecture, beyond slogans.
Vulnerability scanning and automation
Tool familiarity matters, but the bigger signal is automation and triage maturity:
- How findings are deduplicated, prioritised, and routed
- SLAs for remediation, and exceptions governance
- Dependency and supply-chain scanning approach
- Automation that avoids “alert fatigue” while improving outcomes
Compliance integration (NIS2, ISO 27001)
In 2026, DevSecOps engineers are often asked to translate compliance needs into engineering evidence:
- Mapping controls to pipeline checks and logs
- Audit-friendly artefact trails (who changed what, when, and why)
- Segregation of duties and access controls
- Secure SDLC requirements
This is where DevSecOps becomes a force multiplier for information security services and customer trust.
DevSecOps Salary Benchmarks in Europe (2026 Overview)
DevSecOps compensation varies heavily by seniority, cloud depth, and whether the role is platform-led or security-led. The ranges below are indicative base salary levels commonly used for budgeting in 2026, excluding bonuses and equity (which can be material in startups).
Seniority ranges (base salary)
- Junior DevSecOps / Security-minded DevOps (0 to 2 years relevant experience): €55k to €80k (or £45k to £70k in the UK)
- Mid-level DevSecOps Engineer (3 to 5 years): €80k to €115k (or £70k to £105k)
- Senior DevSecOps Engineer / Lead (6+ years, owns pipeline and cloud security design): €115k to €160k+ (or £105k to £150k+)
Germany vs UK vs Netherlands
- Germany: strong demand from regulated industries and industrial cloud migration. Senior profiles commonly sit in the €120k to €165k+ band depending on location and scope.
- UK: London remains highly competitive. Senior base salaries frequently reach £120k to £150k+ for genuine hybrid profiles.
- Netherlands: strong cloud and security clusters around Amsterdam, Utrecht, Eindhoven. Senior base salaries often land in €110k to €155k+, with premiums for deep Kubernetes security or cloud identity expertise.
For Germany-specific budgeting, use Optima’s Cybersecurity salary guide Germany 2026 as a broader reference point across cloud security, DevSecOps, SOC, and GRC.
Startup vs enterprise compensation
- Startups and scale-ups may offer lower base but stronger equity, and wider scope (build from scratch, higher autonomy).
- Enterprises often offer stronger benefits, more stability, and sometimes higher base for senior hires, but with narrower scope and more governance overhead.
Remote salary impact
Remote hiring can widen the talent pool, but it does not automatically reduce cost for high-calibre DevSecOps. Top candidates price against global opportunities, especially if they have AWS, Azure, or GCP depth plus proven Kubernetes security.
Common DevSecOps Hiring Challenges
Most failed DevSecOps searches are not caused by “lack of applicants.” They fail because the role definition, evaluation, and closing mechanics are not designed for a scarce hybrid market.
Technical assessment complexity
Generic DevOps interviews miss security judgement, and generic security interviews miss delivery capability. You need evidence that the candidate can secure CI/CD pipelines, containers, and cloud controls in real engineering conditions.
Misalignment between DevOps and Security teams
If DevOps wants speed and security wants gates, candidates sense internal tension. Strong DevSecOps engineers avoid environments where they will become a “pipeline police officer” without executive support.
Long hiring cycles
Hybrid talent does not wait. If your process runs 6 to 10 weeks, you often end up with late-stage dropouts, counter-offers, or “we like them but need one more round.”
Counter-offers and retention risk
DevSecOps engineers frequently receive retention offers because they hold institutional knowledge of pipeline design and cloud controls. Plan for counter-offers early by building a compelling scope and a crisp offer process.
Cross-border employment challenges
Cross-border recruitment adds real friction: local contracts, tax and payroll models, data access constraints, and background screening expectations. These issues are solvable, but they must be addressed early, not after the final interview.
For an adjacent view on the wider cloud security market, see Optima’s Cloud security hiring trends in Europe.
How to Structure a DevSecOps Hiring Strategy
Below is a decision-ready structure you can use as a DevSecOps hiring guide in Europe. It is designed to reduce time-to-hire without lowering the security bar.
Define Cloud Risk Exposure
Start with your risk reality, not a generic job description:
- Which cloud platforms (AWS, Azure, GCP) are in scope, and which services are mission-critical?
- Are you primarily protecting identity, network, build systems, production runtime, or all of the above?
- Do you need hardening and prevention, or detection and response, or both?
This should produce a one-page “risk and control charter” that candidates can react to. It also prevents hiring a tool operator when you actually need an architecture-level engineer.
Align DevOps & Security Stakeholders
Treat this as a cross-functional hire with shared ownership:
- Agree on who owns the pipeline, who owns policies, and how exceptions are handled.
- Decide where DevSecOps sits organisationally (platform team, security engineering, or a hybrid model).
- Align on metrics (deployment frequency plus security outcomes such as vulnerability SLAs and policy compliance rates).
This alignment is also where you connect hiring to NIS2 and ISO 27001 evidence requirements. If you need a deeper compliance lens, see Optima’s analysis of the NIS2 Directive impact on cybersecurity hiring.
Standardise Technical Evaluation
You need a repeatable assessment that produces comparable evidence across candidates. A strong structure is:
- A short technical screen focused on cloud security fundamentals and CI/CD security
- A work-sample that mirrors your environment (for example, review a Terraform change plus propose pipeline gates)
- A systems interview on Kubernetes and runtime controls
- A stakeholder interview to assess influence, collaboration, and security mindset
Keep the work-sample bounded (60 to 90 minutes) and discuss it live. The goal is not free labour, it is decision-quality evidence.
Align Compensation to Market Reality
Before you launch the search:
- Benchmark your band against the seniority level you actually need.
- Decide your position on remote flexibility, and whether you can hire cross-border.
- Define what you can trade (scope, autonomy, learning budget, equity, bonus) if your base salary ceiling is fixed.
If you only pay “DevOps rates” for a DevSecOps role, you will either lose strong candidates or hire someone who cannot own security outcomes.
Reduce Time-to-Hire Through Specialized Recruitment
In a thin market, speed is strategy, but it must be disciplined speed. Specialist recruiters can reduce time-to-hire by:
- Mapping passive talent across Europe, including candidates not responding to adverts
- Pre-qualifying hybrid capability with role-relevant technical depth
- Running cross-border recruitment with an informed view of local expectations
- Managing offer dynamics, counter-offers, and start date risk
The practical value is not “more CVs.” It is a tighter shortlist with higher evidence density and fewer late-stage surprises.
Recruitment Agency vs In-House Hiring for DevSecOps Roles
In-house hiring can work well when you have a strong employer brand, internal sourcing capacity, and the ability to run fast technical assessment loops. It is often the right choice for repeatable mid-level hiring where the talent pool is reachable through inbound channels.
A specialist recruitment partner becomes more valuable when the role is business-critical and the market is thin:
- Access to passive talent: many senior DevSecOps engineers do not apply to job adverts, they move via trusted networks.
- Cross-border sourcing: if you need to hire outside your current entity footprint, you need sourcing reach plus practical knowledge of cross-border constraints.
- Leadership-level hires: Head of DevSecOps, Platform Security Lead, or senior cloud security engineering roles often require confidential market mapping.
- Confidential hiring: when internal change, incident recovery, or a transformation programme needs discretion.
- Speed: agencies can compress time in sourcing and initial qualification, especially when internal teams are stretched.
The decision is not ideological. It is an ROI question: what is the cost of leaving cloud security gaps open for an extra quarter, or slowing product delivery because security controls are not industrialised?
Frequently Asked Questions (Minimum 6)
What does a DevSecOps engineer do? A DevSecOps engineer embeds security into the software delivery lifecycle. In practice, that means building secure CI/CD pipelines, integrating automated testing (code, dependencies, containers, IaC), setting secure defaults for cloud platforms, and improving visibility through logging and monitoring. They often work closely with platform teams, developers, and security leadership to define policy gates and exception handling. The best DevSecOps engineers also shape behaviour, they make secure delivery the easiest path, rather than relying on manual approvals.
Is DevSecOps in high demand in Europe? Yes. Demand is being pulled by cloud-native adoption (Kubernetes, Docker, IaC), multi-cloud complexity, and board-level risk pressure. In 2026, many European organisations are also strengthening security governance and engineering evidence because of frameworks like ISO 27001 and the operational expectations associated with NIS2. This combination increases demand for engineers who can ship quickly and safely. The result is a persistent DevSecOps talent shortage, especially for senior profiles who have scaled secure delivery across multiple teams.
How much do DevSecOps engineers earn in Europe? Compensation depends on scope (pipeline security vs platform security), cloud depth (AWS, Azure, GCP), and seniority. As a budgeting baseline, junior profiles often land around €55k to €80k, mid-level around €80k to €115k, and senior roles frequently €115k to €160k+ (UK senior roles can reach £120k to £150k+ in competitive markets). Equity and bonuses can materially change total compensation in startups. Remote work can widen options, but top hybrid profiles still price against global demand.
Why is DevSecOps hiring difficult? It is difficult because the role is genuinely hybrid. Many DevOps engineers have limited security depth, and many security engineers have limited delivery and automation depth. On top of that, DevSecOps requires judgement under pressure: prioritising vulnerabilities, designing guardrails that do not break developer velocity, and producing audit-ready evidence. Senior candidates are also heavily retained by employers because they understand critical systems and security controls. Finally, long hiring cycles increase the likelihood of counter-offers and late-stage dropouts.
Do companies need specialised recruiters for DevSecOps? Not always, but specialist support becomes valuable when the hire is business-critical, senior, or cross-border. A specialised recruiter can market-map passive candidates, pre-qualify the hybrid skill set with more accuracy, and manage offer dynamics in a competitive salary environment. They can also help you refine the role so it is attractive to the right profiles (scope, autonomy, risk mandate), and reduce time-to-hire through a disciplined shortlist process. For many CTOs and CISOs, the goal is risk reduction and delivery continuity, not simply filling a vacancy.
How long does it take to hire DevSecOps engineers in Europe? Timelines vary, but DevSecOps roles often take longer than standard DevOps positions because assessment must cover cloud security, pipeline design, and collaboration skills. If you run a tight process and have compensation aligned to market, you can often reach offer stage in 3 to 5 weeks. If stakeholders are misaligned or interviews are unstructured, searches can drift to 8+ weeks and lose candidates to counter-offers. The single biggest controllable variable is decision speed paired with evidence-based evaluation.
Conclusion
DevSecOps has become a strategic hiring priority in Europe because modern delivery stacks (CI/CD pipelines, Kubernetes, Docker, IaC, multi-cloud) create a security surface area that cannot be controlled through policy alone. In 2026, regulatory pressure such as NIS2 expectations, plus ongoing ISO 27001-driven customer requirements, pushes organisations toward security that is continuous, automated, and auditable.
The challenge is that DevSecOps hiring is structurally complex. You are recruiting a rare hybrid profile at a time of cybersecurity talent shortage and salary competitiveness, often while trying to reduce time-to-hire.
If you want a hiring plan built around risk exposure, technical evidence, and cross-border recruitment realities, Optima Search Europe can support market mapping and structured search for DevSecOps and cloud security roles across Europe. Learn more via the Cybersecurity recruitment in Europe guide, or connect with the team to discuss a role brief and current market conditions.

